Ethereum (ETH) users are finding themselves in a bit of a pickle, as address-poisoning attacks have spiked. Yes, you heard that right-“spiked”-just like the enthusiasm of a cat seeing a cucumber for the first time. And the culprit? Dust-transfer transactions are flooding in, almost like an overzealous delivery person.
This whole mess comes after the December 2025 Fusaka upgrade, which kindly lowered transaction fees. A thoughtful gesture, of course-who doesn’t like a good discount? But, as is the custom in the wild west of the internet, where there’s an opportunity, there are also those lovely ‘malicious actors’ ready to make a quick buck. And guess what they’ve been doing? Sending fraudulent transactions, obviously.
How Address Poisoning Exploits Transaction History
Ah, address poisoning! It’s a scam as charming as it sounds. The attackers create wallet addresses that look eerily similar to legitimate ones. The next step? They send tiny, almost insignificant transactions (or ‘dust transfers’-because, apparently, a little dust never hurt anyone) to their unsuspecting targets.
Now, when a user glances at their transaction history, they see these dust transfers mixed in with their real transactions. Sounds fun, right? But wait-Ethereum addresses are 42 characters long. So, the lazy user (who just checks the first and last few characters) might just copy-paste the poisoned address for their next transfer. Oh dear, how quaint!
Follow us on X to get the latest news as it happens
A victim lost 4,556 ETH (~$12.4M) to one of these attacks. The attacker had been ‘dusting’ the victim’s wallet for two months, all the while mimicking their OTC deposit address. And just when you think it couldn’t get worse, dusting happened just 32 hours before the big loss.
– Specter (@SpecterAnalyst) January 30, 2026
Imagine this: once an address is logged in the victim’s transaction history, they may just use it again for the next big transfer. Oh, the irony-sending funds straight to the scammer’s address. A classic case of mistaken identity.
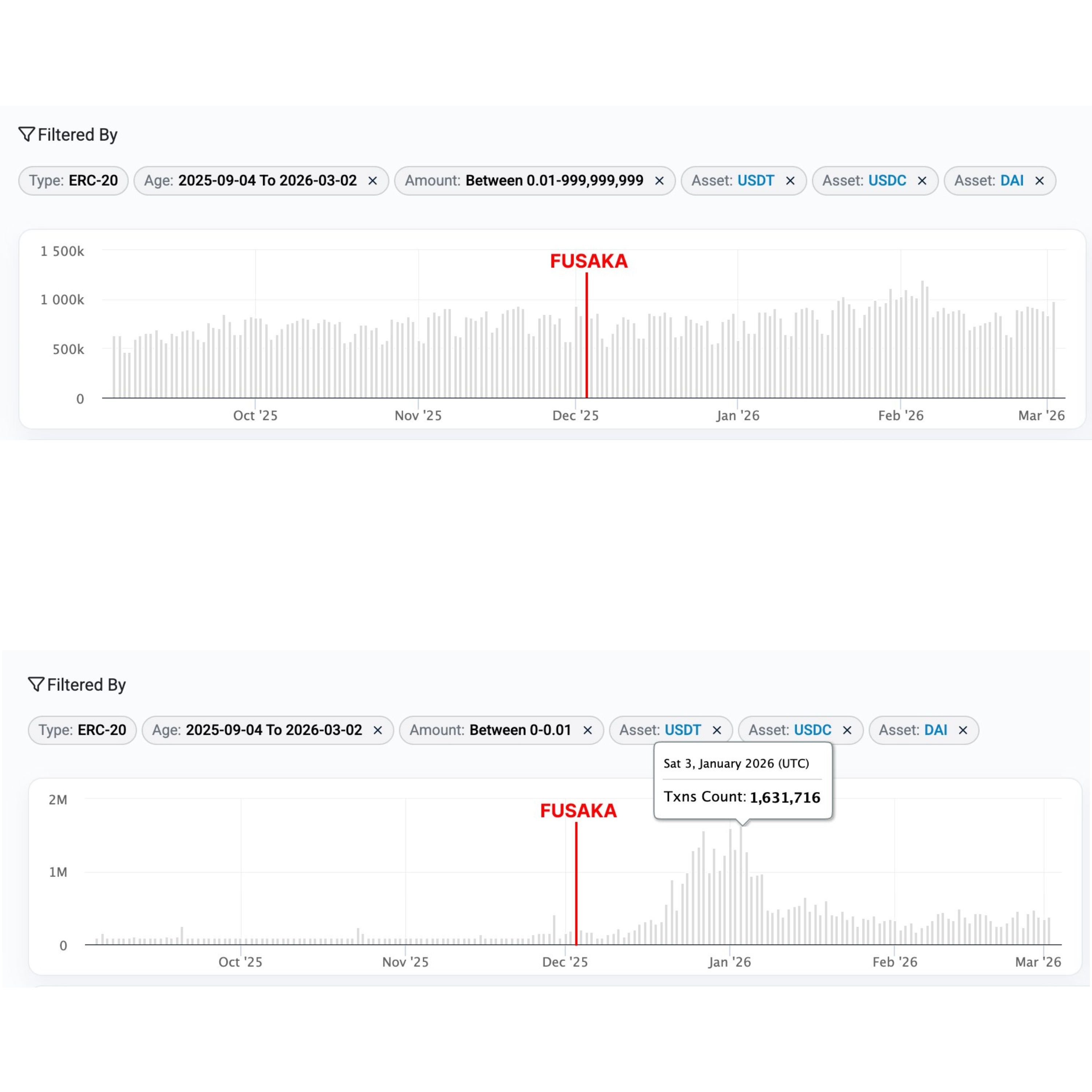
Dust Transfer Activity Explodes After Ethereum’s Fusaka Upgrade, Etherscan Data Shows
Here’s the fun part: this strategy is nothing new. According to Etherscan, from July 2022 to June 2024, about 17 million address poisoning attempts were made. That’s right-17 million attempts to mess with 1.3 million Ethereum users. And the result? A whopping $79.3 million lost in confirmed scams. But don’t worry, folks-the surge in dust transfers after the Fusaka upgrade is truly the icing on the cake.
Let’s talk numbers, shall we? Dust transfers, which are essentially micro-transactions under $0.01 for stablecoins and under 0.00001 ETH for Ether, have exploded. USDT, for instance, went from about 4.2 million dust transfers to nearly 29.9 million-an eye-popping 612% increase. USDC followed suit, rising from 2.6 million to 14.9 million, a 473% surge. DAI was smaller but still noteworthy, going from around 142,000 to over 811,000.
ETH dust transfers, meanwhile, saw a modest 62% increase, moving from 104.5 million to 169.7 million. Ah, the sweet scent of rising numbers.
“Dust transfers (below $0.01) show a clear surge shortly after the Fusaka upgrade, with activity rising sharply before gradually tapering off, though still remaining at an elevated level compared to pre-Fusaka levels. Meanwhile, transfers above $0.01 remained stable,” said Etherscan. Sounds like a classic case of ‘doing just enough to keep the problem alive’.
Despite the fact that the scam’s success rate is a lowly 0.01% (roughly one successful theft per 10,000 attempts), even a single win for the scammer can be quite profitable. It’s like buying a lottery ticket, except, in this case, the ticket costs nothing, and the prize is, well, stolen Ethereum.
“Not all dust transfers are poison transfers. Some of them happen during legitimate activities, like token swaps. However, a rather suspicious portion of them do seem to be poisoning attempts,” said Etherscan. And who’s to say that a little suspicion isn’t fun every now and then?
But of course, it’s not just about the fees. Address poisoning has become a well-oiled machine, with operations increasingly industrialized. Attackers don’t just target one user-they compete with each other to be the first to poison the well, so to speak. Charming, isn’t it?
How to Protect Yourself
For those brave souls venturing into Ethereum’s wild terrain, here are five ways to shield yourself from falling victim to address poisoning:
- Don’t copy addresses from transaction history. Get them from a trusted source-your recipient, a contact list, or, I don’t know, a magic 8-ball?
- Before confirming any transaction, inspect every single character. Don’t just skim the edges, like you’re looking at an Instagram post.
- Use address whitelisting. Save trusted addresses so you don’t accidentally pick a spoofed one.
- If you’re making a big transaction, send a tiny test first. Just a little something to see if everything’s kosher. It’s like a first date-don’t go all in just yet.
- Use wallets with scam detection. Let technology be your friend, not just your wallet’s endless pit of potential heartbreak.
Subscribe to our YouTube channel to watch leaders and journalists provide expert insights
Read More
- Epic Games Store Giving Away $45 Worth of PC Games for Free
- 10 Movies That Were Secretly Sequels
- When Is Hoppers’ Digital & Streaming Release Date?
- Sunday Rose Kidman Urban Describes Mom Nicole Kidman In Rare Interview
- 32 Kids Movies From The ’90s I Still Like Despite Being Kind Of Terrible
- 40 Inspiring Optimus Prime Quotes
- 7 Best Animated Horror TV Shows
- Best Werewolf Movies (October 2025)
- 5 Best Superman-Centric Crossover Events
- All The Howl Propaganda Speaker in Borderlands 4
2026-03-13 09:24