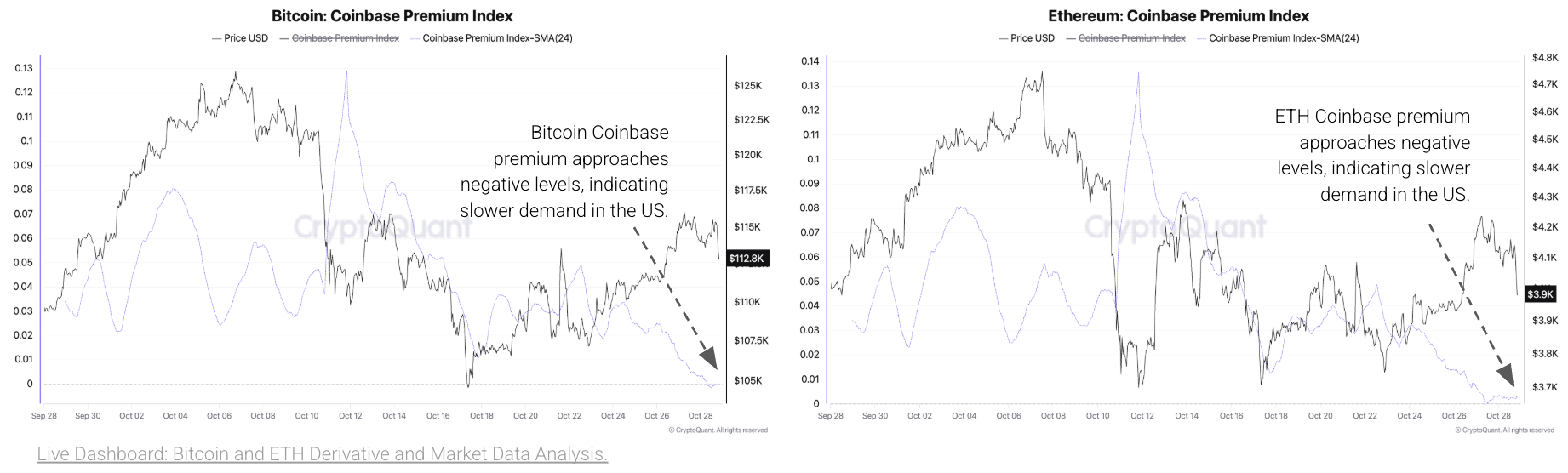
Behold the recent tremor, that cruel correction birthed from the Federal Reserve’s solemn gathering, which has rattled the frail confidence of the masses like a gambler’s last die. Yet, beneath the surface tumult, the omens stir-a shift, inexorable as fate’s decree. The Fed, in its infinite wisdom (or folly?), slices rates by a miserly 25 basis points and vows to cease its quantitative tightening by December 1st. Thus, the era of constriction, that iron yoke upon the neck of liquidity, may at last shatter, heralding-dare we dream?-the dawn of a bull market resurgence, as history’s cycles mock our doubts. 🙄